Services
Focus on your business. Outsource to a strong cybersecurity platform to build trust, reduce risk and build trust while positively impacting your time, people & bottom line.
Cybersecurity-as-a-Service
Making security accessible and achievable for all types of entry-level businesses.
Problem :
We are living in a vendor-centric, tool-crazed industry. Security vendors profit off customer failure with a reactive approach. There is a cybersecurity skill gap shortage, and customers are losing.
Solution :
A simple cybersecurity subscription program geared for start-ups and small-to-midsized businesses with the goal of fast tracking needed compliance. These businesses need expert people, easy processes which include continuous maintenance, vetted best-of-breed security tools, and an all-inclusive platform to manage your security program in one place.

Cloud Automation & Orchestration
Affordable, secure AWS cloud managed solutions for startups & small enterprises.
Problem :
Cloud complexity is difficult for small teams who have to understand infrastructure problems, operational costs, business outages, and security breaches in their environment.
Solution :
Solve complex problems with simple, streamlined technology and a partner that understands the infrastructure limitations, operational needs and your business goals. Migrate, customize, adopt and monitor. This includes turnkey:
- Deployment Pipelines
- Monitoring Notifications & Logs
- Backup & Restore
- Secrets Management
- Performance Dashboards
- SSH Access to EC2 Instances
- AWS Application APIs
- AWS Console Access

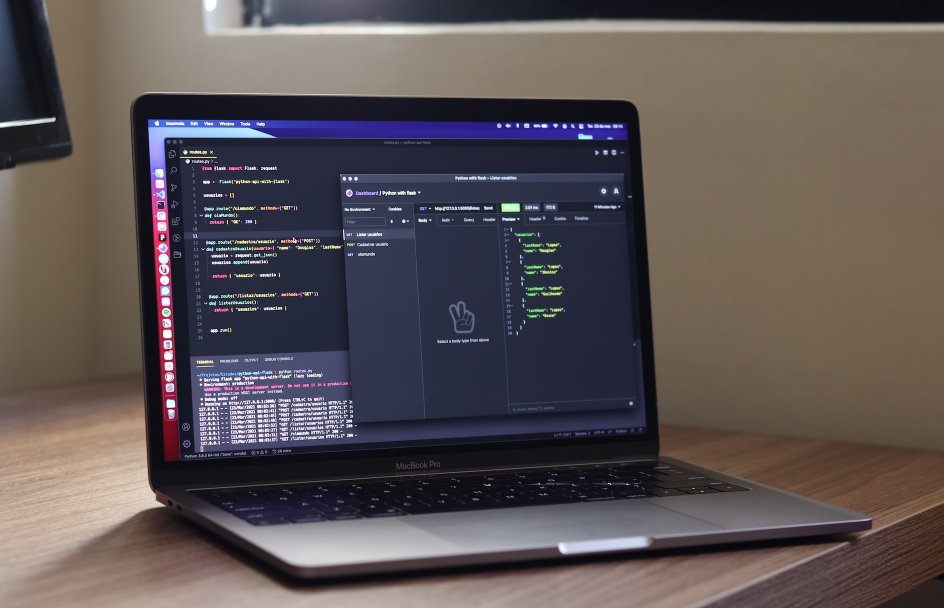
API Security
Detects & Responds to Application Programming Interfaces (API) attacks at runtime.
Problem :
API’s play a vital role in today’s enterprise growth strategies. Organizations are rushing to deploy API’s as fast as they can, often forgetting or minimizing the potential security risks.
Solution :
To protect business & client assets and reputation, it is critical to adopt strategies to maintain the integrity & confidentiality of data that is accessible through APIs. This reframes the concept of API-first. Rather than relying on assumptions as to how your APIs should work, observability tells you how they ARE working by capturing all requests and response details.